Additional information
| Prerequisites | All learners are required to have completed or have the equivalent knowledge corresponding to EXP-100 Exploit Development Essentials. Especially:
|
|---|---|
| Difficulty level | |
| Duration | 90 days |
| Certificate | After passing the OSED exam, candidates receive a title of OffSec Exploit Developer (OSED). |
| Trainer | Authorized OffSec Trainer |
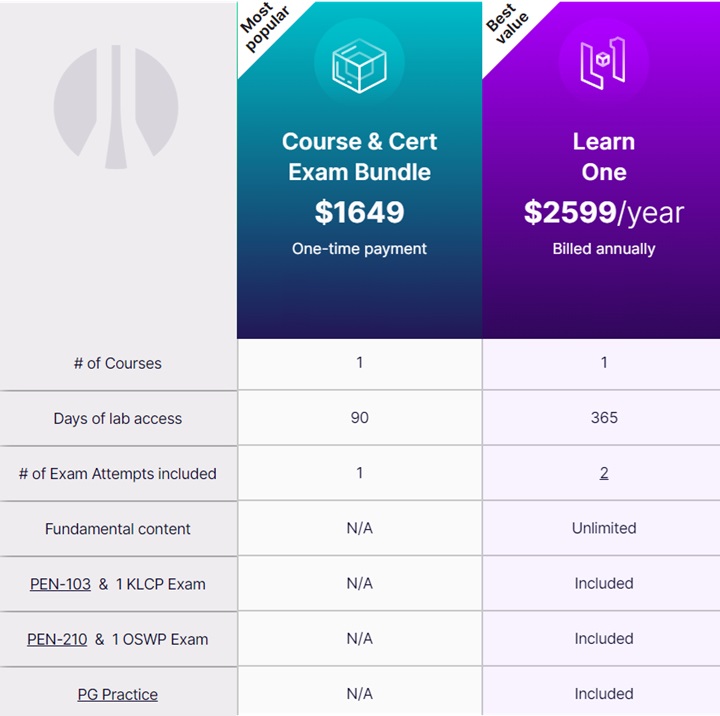
| Additional informations | Course is available as the e-learning product, in two subscription's models:
|
Other training OffSec | Learn Subscriptions
-

OffSec PEN-300 Advanced Evasion Techniques and Breaching Defenses training OffSec
price from: 1749 USD
duration: 90 days
difficulty level: 6 of 6
code: OFFSEC-PEN-300
version: PEN-300
-

OffSec WEB-300 Advanced Web Attacks and Exploitation training OffSec
price from: 1749 USD
duration: 90 days
difficulty level: 6 of 6
code: OFFSEC-WEB-300
version: WEB-300
-

OffSec EXP-312 Advanced macOS Control Bypasses training OffSec
price from: 1749 USD
duration: 90 days
difficulty level: 6 of 6
code: OFFSEC-EXP-312
version: EXP-312
Upcoming OffSec training
-
2025-09-22 Kraków / Virtual Classroom
OffSec PEN-200 Penetration Testing with Kali Linux
hybrid training: HYBRID -
2025-09-22 Virtual Classroom
OffSec PEN-200 Penetration Testing with Kali Linux
-
2025-10-20 Kraków / Virtual Classroom
OffSec PEN-200 Penetration Testing with Kali Linux
hybrid training: HYBRID -
2025-11-17 Warszawa / Virtual Classroom
OffSec PEN-200 Penetration Testing with Kali Linux
hybrid training: HYBRID -
2025-12-01 Kraków / Virtual Classroom
OffSec PEN-200 Penetration Testing with Kali Linux
hybrid training: HYBRID -
2025-12-15 Kraków / Virtual Classroom
OffSec PEN-200 Penetration Testing with Kali Linux
hybrid training: HYBRID -
2025-12-15 Virtual Classroom
OffSec PEN-200 Penetration Testing with Kali Linux